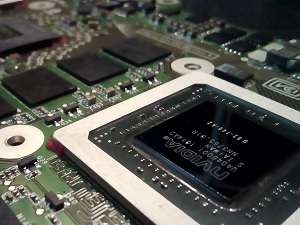
 If you have computers on your corporate network that rely on NVIDIA hardware and software, be advised that the company recently released security updates to address serious security vulnerabilities found in CUDA and GPU Display drivers and Virtual GPU Management software. These are security flaws that could lead to an escalation of privileges, denial of service and arbitrary code execution on both Linux and Windows machines.
If you have computers on your corporate network that rely on NVIDIA hardware and software, be advised that the company recently released security updates to address serious security vulnerabilities found in CUDA and GPU Display drivers and Virtual GPU Management software. These are security flaws that could lead to an escalation of privileges, denial of service and arbitrary code execution on both Linux and Windows machines.
All of the flaws are rated as serious or higher, but it should be noted that all of them require local user access. They cannot be exploited remotely. Once hackers have gained a foothold on a target machine, they could launch attacks designed to abuse these bugs. So it pays to treat the issue seriously and apply the patch as soon as possible.
The good news is that when you install the latest security patch, you'll get fixes for a wide range of issues with severity ratings ranging from 7.8 to 4.4.
Here's what the latest patch addresses (Listed in order of relative severity):
- CVE-2020-5962, CVE-2020-5963, CVE-2020-5968, CVE-2020-5969, CVE-2020-5970, and CVE-2020-5971 (All have a severity rating of 7.8)
- CVE-2020-5964 (Severity rating: 6.5)
- CVE-2020-5965, CVE-2020-5966, CVE-2020-5967, and CVE-2020-5972 (All have a severity rating of 5.5)
- CVE-2020-5973 (Severity rating: 4.4)
If any of the machines on your network utilize GeForce, Quadro, NVS, Tesla GPU drivers, or the Virtual GPU Manager, be sure to grab the latest security patch from NVIDIA's driver download page.
If you're a Windows user and not in the habit of patching your drivers manually, you may also receive Windows GPU display driver 451.55, 446.06, and 443.18 from your hardware vendor. Enterprise users will need to log into the NVIDIA Enterprise Application hub to get the latest updates. However you get them, the important thing is to install them to patch yourself out of harm's way.



